Engineering Sensor Spoofing Protection into the Android Operating System
Authors: Roy Hershkovitz , Yossi Oren
Appeared in: IEEE Access (early access)
Abstract
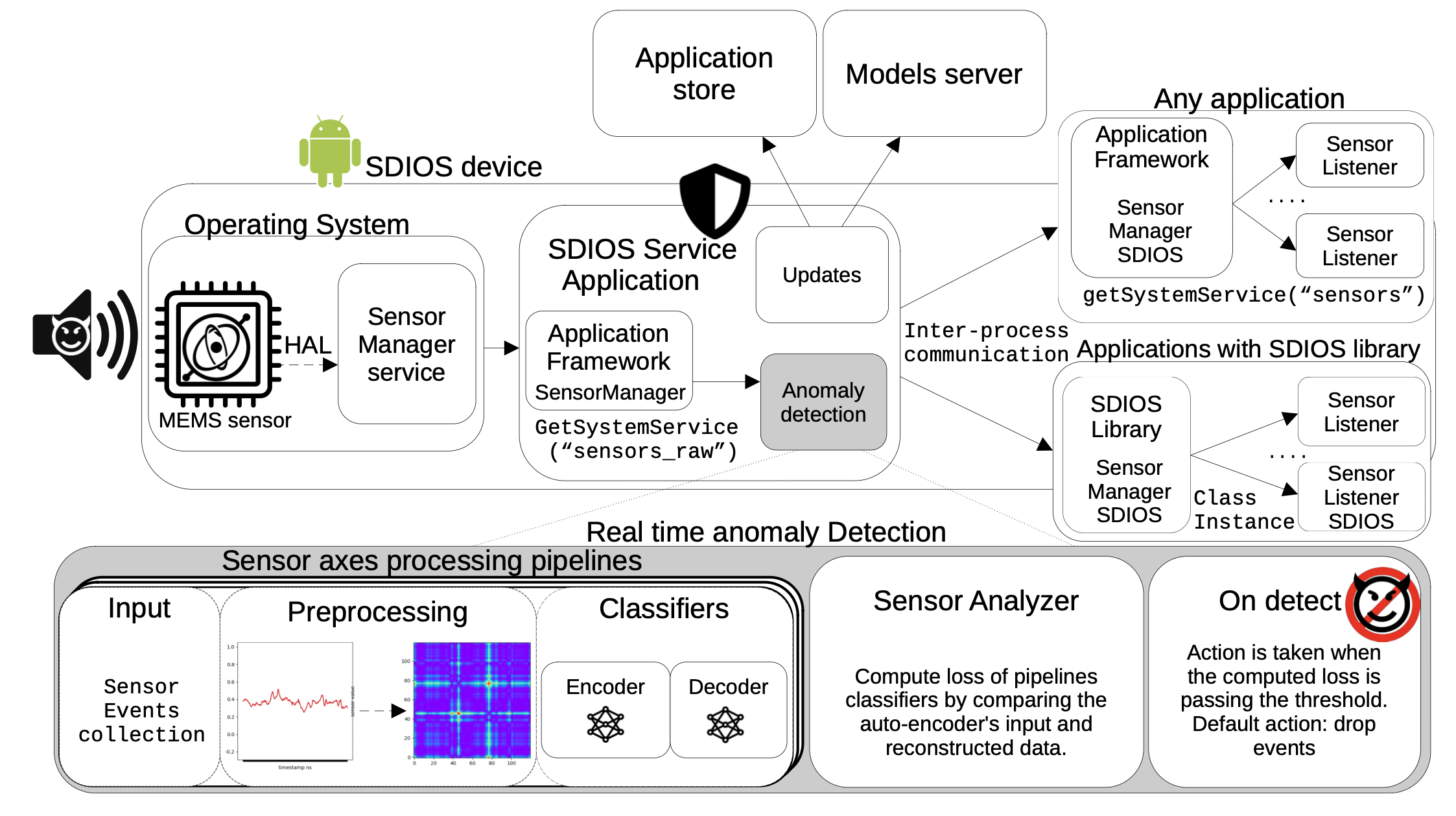
Sensor spoofing attacks are a serious threat to mobile phones, as they can manipulate sensor readings to subvert the behavior of applications that rely on these readings. Previous work has shown how machine learning defenses provide effective protection against sensor spoofing attacks without hardware modification. Unfortunately, these defenses require changes to the applications themselves. In this paper, we present SDIOS (Sensor Defense in the Operating System), an approach that engineers sensor spoofing protection into the operating system level, without requiring any modifications to the applications. At its core, SDIOS incorporates an autoencoder based on a Gramian Angular Field (GAF) representation of the sensor readings. We describe the design and implementation of SDIOS, and evaluate its performance and compatibility on a variety of devices. Our results show that SDIOS is able to detect and prevent sensor spoofing attacks in real time, while retaining compatibility with existing applications, but that its performance impact is significant, especially on resource-constrained devices where the machine learning pipeline is run on the central processing unit (CPU).