HammerScope: Observing DRAM Power Consumption Using Rowhammer
Authors: Yaakov Cohen , Kevin Sam Tharayil , Arie Haenel , Daniel Genkin , Angelos D. Keromytis , Yossi Oren , Yuval Yarom
Appeared in: 29th ACM Conference on Computer and Communications Security (CCS), 2022
Abstract
The constant reduction in memory cell sizes has increased memory density and reduced power consumption, but has also affected its reliability. The Rowhammer attack exploits this reduced reliability to induce bit flips in memory, without directly accessing these bits. Most Rowhammer attacks target software integrity, but some recent attacks demonstrated its use for compromising confidentiality.
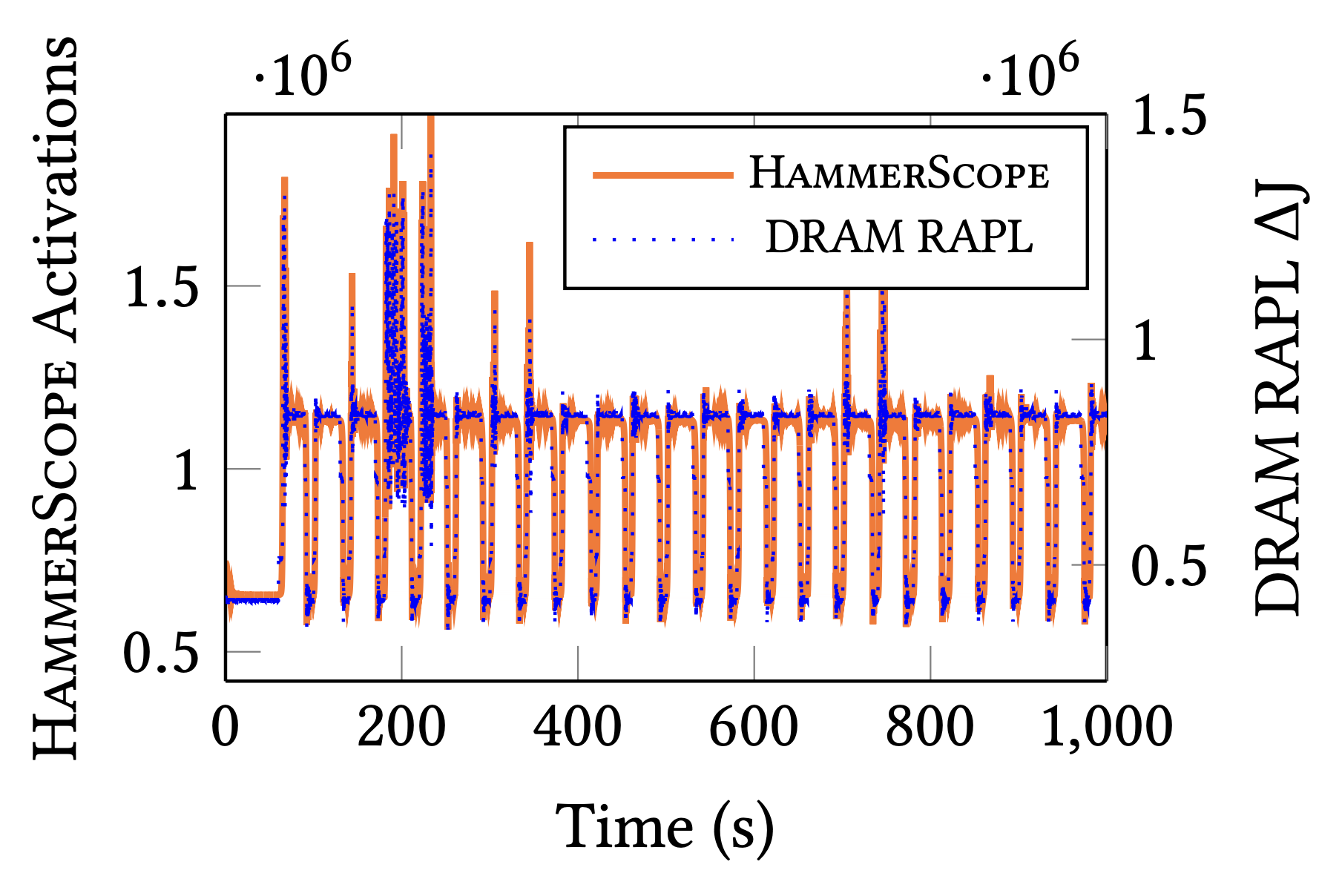
Continuing this trend, in this paper we observe that the Rowhammer attack strongly correlates with the memory instantaneous power consumption. We exploit this observation to design HammerScope, a Rowhammer-based attack technique for measuring the power consumption of the memory unit. Because the power consumption correlates with the level of activity of the memory, HammerScope allows an attacker to infer memory activity.
To demonstrate the offensive capabilities of HammerScope, we use it to mount three information leakage attacks. We first show that HammerScope can be used to break kernel address-space layout randomization (KASLR). Our second attack uses memory activity as a covert channel for a Spectre attack, allowing us to leak information from the operating system kernel. Finally, we demonstrate the use of HammerScope for performing website fingerprinting, compromising user privacy. Our work demonstrates the importance of finding systematic solutions for RowHammer attacks.