Website Fingerprinting Through the Cache Occupancy Channel and its Real World Practicality
Authors: Anatoly Shusterman , Zohar Avraham , Eliezer Croitoru , Yarden Haskal , Lachlan Kang , Dvir Levi , Yosef Meltser , Prateek Mittal , Yossi Oren , Yuval Yarom
Appeared in: IEEE Transactions on Dependable and Secure Computing Volume 18, Issue 5, September 2021
Abstract
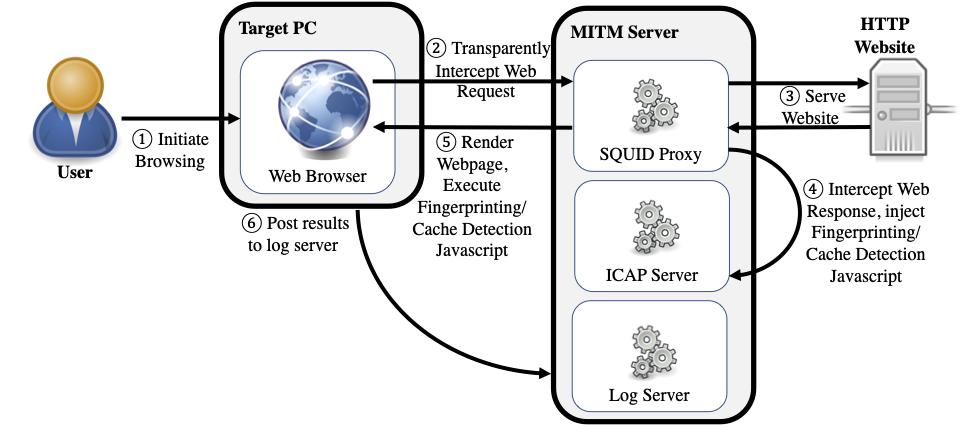
Website fingerprinting attacks use statistical analysis on network traffic to compromise user privacy. The classical attack model used to evaluate website fingerprinting attacks assumes an on-path adversary, who observes traffic traveling between the user’s computer and the network.
In this work we investigate a different attack model, in which the adversary sends JavaScript code to the target user’s computer. This code mounts a cache side-channel attack to identify other websites being browsed. Using machine learning techniques to classify traces of cache activity, we achieve high classification accuracy in both the open-world and the closed-world models. Our attack is more resistant than network-based fingerprinting to the effects of response caching, and resilient both to network- based defenses and to side-channel countermeasures. We carry out a real-world evaluation of several aspects of our attack, exploring the impact of the changes in websites and browsers over time, as well as of the attacker’s ability to guess the software and hardware configuration of the target user’s computer.
To protect against cache-based website fingerprinting, new defense mechanisms must be introduced to privacy-sensitive browsers and websites. We investigate one such mechanism, and show that it reduces the effectiveness of the attack and completely eliminates it when used in the Tor Browser.
Note: This is the extended version of our Usenix Security 2019 paper, which adds a real-world evaluation.
Dataset Availability
The dataset used in this paper is publicly available under a CC-BY license on IEEE DataPort.